Antonios Gogios
Software Engineer
Disassembly Analysis Demo: Executable Patching
2015
This is a simple disassembly analysis aimed at altering the behavior of a compiled C++ program I wrote, by patching the resultant executable. The program represents a credentials check -- specifically a simplistic password prompt. For illustration purposes, embedded string constants and no hashing is used, simplifying the process.
Illustrated Overview

Left: The program "Antonis_pswd.exe" requests a password, looping indefinitely until the correct password, "Antonis_pswd", is input.
The patched version of the program prompts the user for a password, although accepts any input as correct (e.g. "abc" in this example).
The patch alters 2 bytes in the executable, making the condition check for the password always return true.
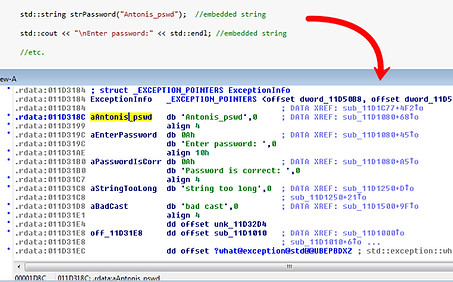
Left: The C++ program I wrote here intentionally contains embedded string constants and an unhashed password. As expected, the embedded strings are located in the .rdata section of this PE file.
Examining the embedded strings allows easy identification of the relevant control flow for the password check.

Left: After locating the relevant condition check in the disassembly listing, the flow is altered so that any input string is considered correct.
The changes performed on the original executable amount to the 2 bytes illustrated in the image.